Technology Policy Template
Document content
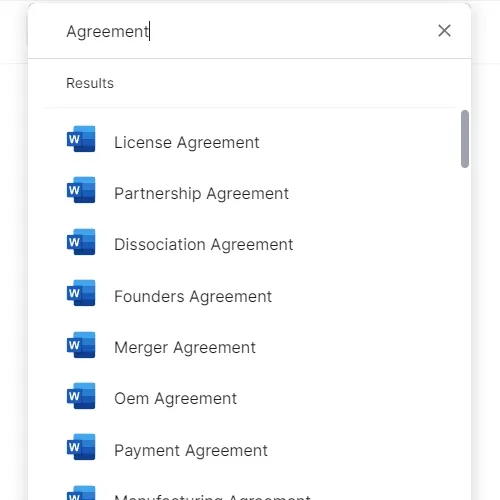
This technology policy template has 3 pages and is a MS Word file type listed under our legal agreements documents.
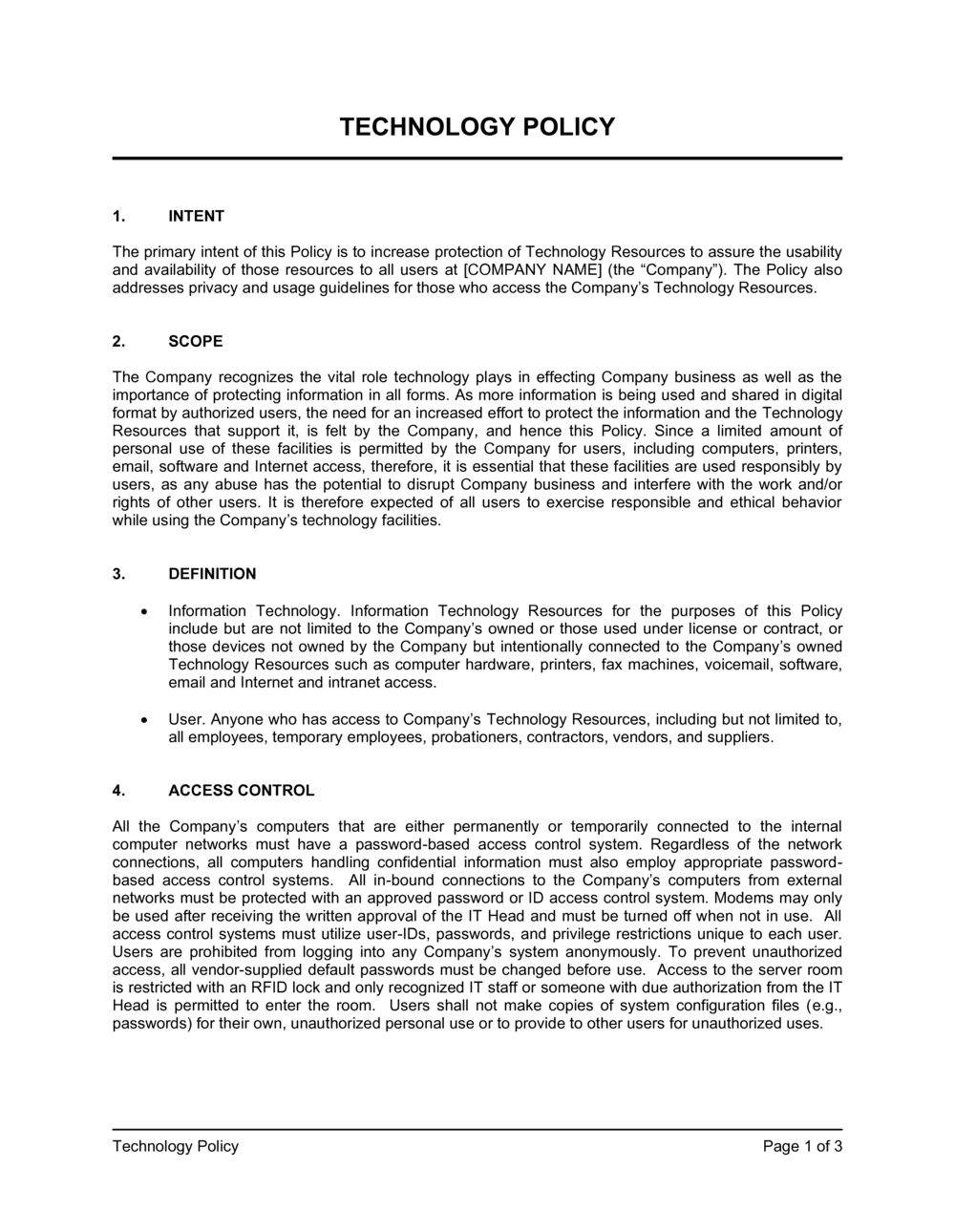
Sample of our technology policy template:
TECHNOLOGY POLICY INTENT The primary intent of this Policy is to increase protection of Technology Resources to assure the usability and availability of those resources to all users at [COMPANY NAME] (the "Company"). The Policy also addresses privacy and usage guidelines for those who access the Company's Technology Resources. SCOPE The Company recognizes the vital role technology plays in effecting Company business as well as the importance of protecting information in all forms. As more information is being used and shared in digital format by authorized users, the need for an increased effort to protect the information and the Technology Resources that support it, is felt by the Company, and hence this Policy. Since a limited amount of personal use of these facilities is permitted by the Company for users, including computers, printers, email, software and Internet access, therefore, it is essential that these facilities are used responsibly by users, as any abuse has the potential to disrupt Company business and interfere with the work and/or rights of other users. It is therefore expected of all users to exercise responsible and ethical behavior while using the Company's technology facilities. DEFINITION Information Technology. Information Technology Resources for the purposes of this Policy include but are not limited to the Company's owned or those used under license or contract, or those devices not owned by the Company but intentionally connected to the Company's owned Technology Resources such as computer hardware, printers, fax machines, voicemail, software, email and Internet and intranet access. User. Anyone who has access to Company's Technology Resources, including but not limited to, all employees, temporary employees, probationers, contractors, vendors, and suppliers. ACCESS CONTROL All the Company's computers that are either permanently or temporarily connected to the internal computer networks must have a password-based access control system. Regardless of the network connections, all computers handling confidential information must also employ appropriate password-based access control systems. All in-bound connections to the Company's computers from external networks must be protected with an approved password or ID access control system. Modems may only be used after receiving the written approval of the IT Head and must be turned off when not in use. All access control systems must utilize user-IDs, passwords, and privilege restrictions unique to each user. Users are prohibited from logging into any Company's system anonymously. To prevent unauthorized access, all vendor-supplied default passwords must be changed before use. Access to the server room is restricted with an RFID lock and only recognized IT staff or someone with due authorization from the IT Head is permitted to enter the room. Users shall not make copies of system configuration files (e.g., passwords) for their own, unauthorized personal use or to provide to other users for unauthorized uses.
3,000+ Templates & Tools to Help You Start, Run & Grow Your Business

Document content
This technology policy template has 3 pages and is a MS Word file type listed under our legal agreements documents.
Sample of our technology policy template:
TECHNOLOGY POLICY INTENT The primary intent of this Policy is to increase protection of Technology Resources to assure the usability and availability of those resources to all users at [COMPANY NAME] (the "Company"). The Policy also addresses privacy and usage guidelines for those who access the Company's Technology Resources. SCOPE The Company recognizes the vital role technology plays in effecting Company business as well as the importance of protecting information in all forms. As more information is being used and shared in digital format by authorized users, the need for an increased effort to protect the information and the Technology Resources that support it, is felt by the Company, and hence this Policy. Since a limited amount of personal use of these facilities is permitted by the Company for users, including computers, printers, email, software and Internet access, therefore, it is essential that these facilities are used responsibly by users, as any abuse has the potential to disrupt Company business and interfere with the work and/or rights of other users. It is therefore expected of all users to exercise responsible and ethical behavior while using the Company's technology facilities. DEFINITION Information Technology. Information Technology Resources for the purposes of this Policy include but are not limited to the Company's owned or those used under license or contract, or those devices not owned by the Company but intentionally connected to the Company's owned Technology Resources such as computer hardware, printers, fax machines, voicemail, software, email and Internet and intranet access. User. Anyone who has access to Company's Technology Resources, including but not limited to, all employees, temporary employees, probationers, contractors, vendors, and suppliers. ACCESS CONTROL All the Company's computers that are either permanently or temporarily connected to the internal computer networks must have a password-based access control system. Regardless of the network connections, all computers handling confidential information must also employ appropriate password-based access control systems. All in-bound connections to the Company's computers from external networks must be protected with an approved password or ID access control system. Modems may only be used after receiving the written approval of the IT Head and must be turned off when not in use. All access control systems must utilize user-IDs, passwords, and privilege restrictions unique to each user. Users are prohibited from logging into any Company's system anonymously. To prevent unauthorized access, all vendor-supplied default passwords must be changed before use. Access to the server room is restricted with an RFID lock and only recognized IT staff or someone with due authorization from the IT Head is permitted to enter the room. Users shall not make copies of system configuration files (e.g., passwords) for their own, unauthorized personal use or to provide to other users for unauthorized uses.
Easily Create Any Business Document You Need in Minutes.
Access over 3,000+ business and legal templates for any business task, project or initiative.
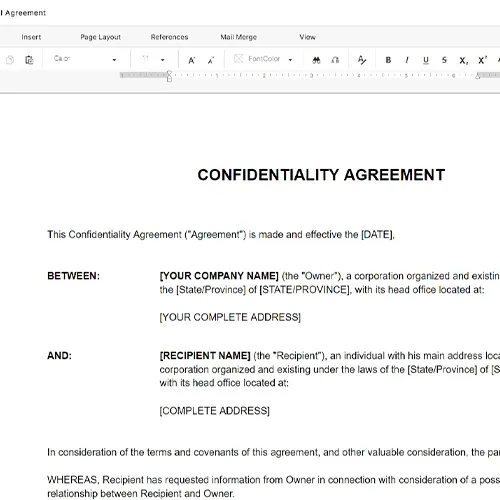
Customize your ready-made business document template and save it in the cloud.
Share your files and folders with your team. Create a space of seamless collaboration.
Templates and Tools to Manage Every Aspect of Your Business.
Business in a Box Covers Every Business Department
Includes 16 Types of Business Documents You Need
and Achieve Your Business Goals Faster.
